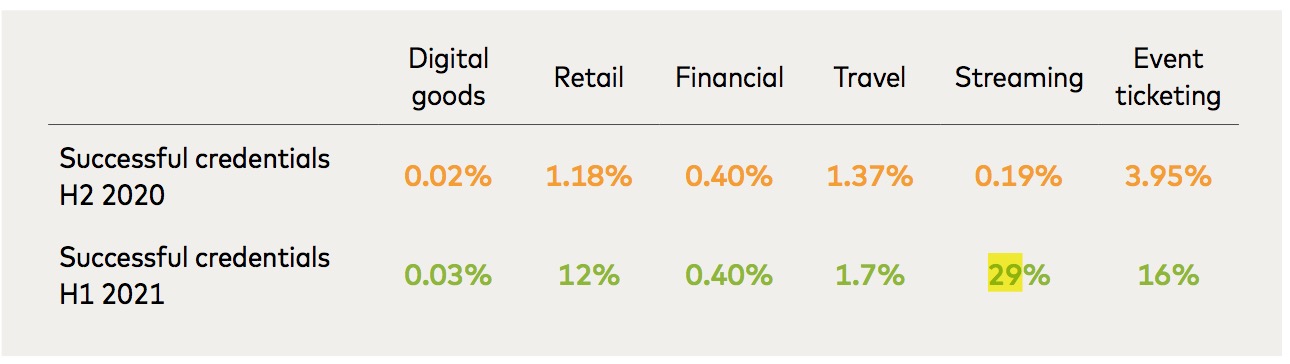
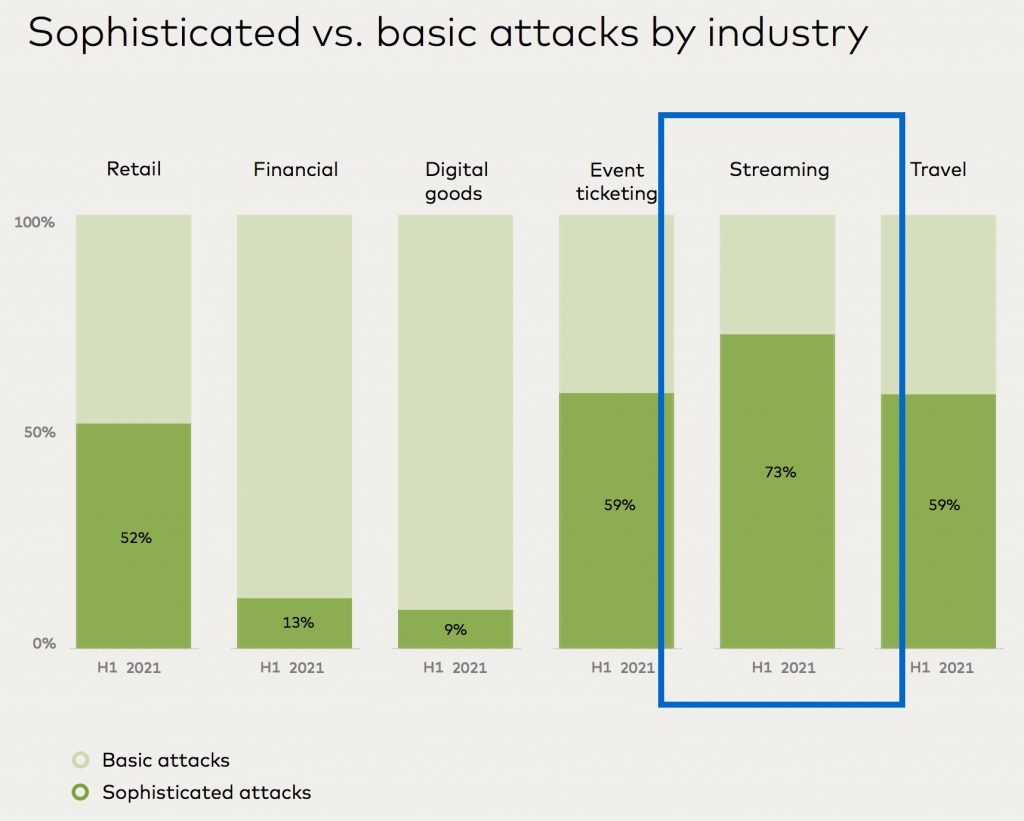
The streaming industry was the most targeted with sophisticated attacks in the first half of 2021, as 73% of attacks used tools that evaded detection, according to a report by NuData Security and Master Card Technologies Canada which measured consumer cyberattacks for the first half of 2021 (January 1 through June 30). The success rate in penetrating streaming accounts was up more than a hundred-fold, from 0.19% to 29%
As streaming usage increased exponentially during the pandemic, more people became vulnerable.
Attackers have responded to this situation in several ways:
- Attacks have become more sophisticated.
- Testing of stolen credentials has increased.
- Successful attack rates increased dramatically.
Card cycling attacks increased by 54% as fraudsters test the stolen data that they had purchased. MasterCard Canada defines card cycling a a type of credential stuffing attack that tests the validity of stolen payment information by making hundreds or thousands of micro-purchases using different payment information each time. Bots record which cards are declined and which are approved. At the end of the process, the fraudster has a list of valid credit card numbers they can use or resell.
Request the report H1 2021: Fraud Risk at a Glance – NuData analysts report on cybersecurity trends (NuData Security / MasterCard Technologies Canada)
Why it matters
Fraudsters are getting better at account theft, which can result in financial theft and the theft of personal information, as well as opening avenues for software-based attacks at later times.
This report found that four factors are at work:
- Data breaches exist that take a long time to discover, if they are discovered at all
- Attackers are prioritizing rapidly evolving industries
- Phishing has increased – by about 20% in 2020 over 2019
- Fake accounts are being created from stolen credentials that work successfully
Quoting the report, “The average credential success rate of an automated attack at login is usually low — less than 2%. By contrast, legitimate users only mistype their passwords occasionally, giving them success rates in the 70% to 90% range.
That’s why some companies protect their login pages with simple rules that identify any user with a high number of failed logins as a potential bad actor. By artificially raising the credential success rate, an attacker can get around these rules and improve their chances of succeeding in the attack.”












