Phase three of Operation Endgame’s takedown action, conducted between November 10 and November 13, 2025, targeted Rhadamanthys, one of the biggest infostealers, the Remote Access Trojan VenomRAT, and the botnet Elysium, all of which played a key role in international cybercrime. The main suspect for VenomRAT was also arrested in Greece.
The infrastructure that was dismantled during the action days was responsible for inflicting malware on hundreds of thousands of victims worldwide.
Criminal services and their criminal users were targeted. These users were directly contacted by the police and asked to share relevant information regarding infostealers via the Operation Endgame Telegram channel. In addition, the failing criminal services are exposed via the Operation Endgame website.
International coordination
Coordinated by Europol and Eurojust, Operation Endgame is a joint effort between law enforcement and judicial authorities of Australia, Belgium, Canada, Denmark, France, Germany, Greece, Lithuania, the Netherlands, the United Kingdom and the United States to tackle ransomware enablers.
More than 30 national and international public and private parties are supporting the actions. Additional contributions were made by private partners Cryptolaemus, Shadowserver and RoLR, Spycloud, Cymru, Proofpoint, Crowdstrike, Lumen, Abuse.ch, HaveIBeenPwned, Spamhaus, DIVD, Trellix and Bitdefender.
Takedown details
Europol facilitated the information exchange and provided analytical, crypto-tracing and forensic support to the investigation. To support the coordination of the operation, Europol organised and coordinated calls with all the countries as well as an operational sprint at its headquarters.
Over 100 law enforcement officers from Australia, Canada, Denmark, France, Germany, Greece, the Netherlands and the United States supported the coordination of the operational actions from the command post at Europol. The command post facilitated the exchange of intelligence on seized servers, suspects, and the transfer of seized data. Eurojust also assisted with the execution of a European Arrest Warrant and European Investigation Orders.
The coordinated actions led to:
- 1 arrest in Greece
- 11 locations searched (1 in Germany, 1 in Greece, and 9 in the Netherlands)
- Over 1 025 servers taken down or disrupted worldwide
- 20 domains seized
Remediation
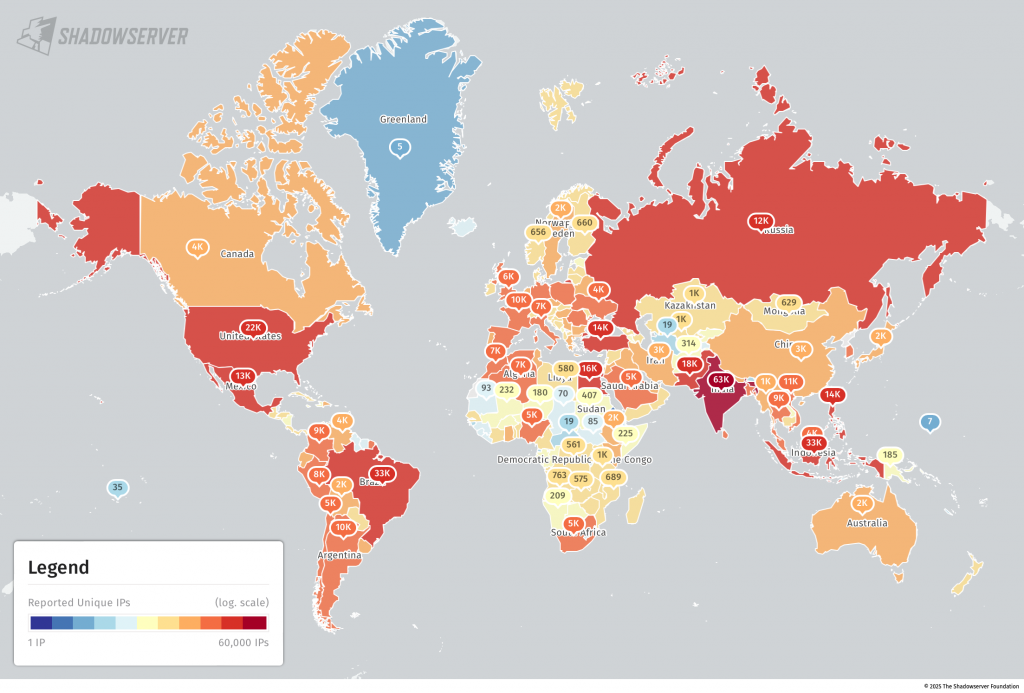
According to the Shadow Server Foundation, targets successfully disrupted included IcedID, SystemBC, Pikabot, Smokeloader and Bumblebee. Data from seized criminal backends was shared with Shadowserver, to distribute to 201 National CSIRTs in 175 countries and over 10,000 network owners globally, to aid in victim identification and remediation. CSIRT is the Computer Security Incident Response Team, which is tasked with responding to cybersecurity incidents and operates globally.
Understanding the risks
The Shadow Server Foundation notes that the Rhadamanthys infostealer malware may have been used to drop additional secondary malware on infected systems, so other malware infections may also be active on these systems and require further local remediation efforts. These victim systems may also have been used in historic or recent intrusions and ransomware incidents.
Discovered in 2020, VenomRAT is used to remotely access computers and is generally distributed as malicious attachments in spam emails. Malicious actors obtain it by subscription for $150 per month, according to reporting by Info Security.
TRUSecurity reports that, once installed, VenomRAT uses obfuscated Microsoft Office macro script to download malicious files, then executes functions from library and uses PowerShell scripts for further actions.
Why it matters
The dismantled malware infrastructure consisted of hundreds of thousands of infected computers containing several million stolen credentials. Many of the victims were not aware of the infection of their systems. The main suspect behind the infostealer had access to over 100 000 crypto wallets belonging to these victims, potentially worth millions of euros. Check if your computer has been infected and what to do if so at politie.nl/checkyourhack and haveibeenpwned.com
Further reading
End of the game for cybercrime infrastructure; 1025 servers taken down. Press release. November 13, 2025. Europol.
Rhadamanthys historical bot infections special report. Article. November 13, 2025. Shadow Server Foundation
VenomRAT: A remote access tool with dangerous consequences. Article. November 30, 2021. TRUSecurity, Acronis International
Operation Endgame 3.0 dismantles three major malware networks. Article. November 13, 2025. Info Security Magazine












