While AI has rightfully captured the attention of media & entertainment industry stake-holders, it’s just as important to act on threats and trends across more traditional security measures, says the Trusted Partner Network (TPN).
The TPN’s STAR Report is the first industry study to analyze large-scale security assessment data and track how cyber risks are evolving across the global content supply chain. STAR stands for Security Trends Analytics Readiness. It will be updated annually to highlight security progress across TPN’s 2,000-plus members.
TPN is the film and television industry’s leading content security initiative, and is owned and managed by the MPA, whose studio members are Netflix, Paramount Pictures, Prime Video & Amazon MGM Studios, Sony Pictures, Universal Studios, The Walt Disney Studios, and Warner Bros. Discovery.
Urgent priorities
The report identifies and explains immediate actions that organizations can take to drive security improvements:
- Treat security as a daily responsibility: Service providers should regularly scan, test and quickly remediate known vulnerabilities
- Fix high-risk technical gaps first: Especially software vulnerabilities, and weaknesses linked to security incidents
- Lock down identity & access: Require multi-factor authentication. Regularly review access roles and privileges
- Hold vendors and partners accountable: Clearly define expections in contracts and shared security responsibilities, coordinate multi-vendor oversight, and ask vendors to show evidence of their ability to meet security requirements
- Respond faster when security gaps are foiund: Don’t just document, act and track progress
TPN offers a wide range of programs, practices and documentation to help in this process.
Openings to risk
While most organizations have foundational security technology policies in place, inconsistent day-to-day execution of technical controls is creating systemic and exploitable risk. By analyzing validated TPN security assessments alongside incident-driven Security Alerts, the report shows a clear pattern of control failures that closely match real-world attacks that stem from incomplete or lack of compliance with recommended best practices.
Recent security alerts consistently pointed to the same underlying technical weaknesses across incidents, including:
- Compromised credentials
- Inconsistent multi-factor authentication (MFA)
- Insecure system and cloud configurations
- Delays in patching and vulnerability remediation
In the first quarter of 2026, TPN issued more Security Alerts than in all of 2025, reflecting a sharp increase in credential-based attacks, misconfigurations, and exploitation of un-remediated vulnerabilities. While TPN provides the platform and standards for assessing security, fixing any issues is the responsibility of the organizations being assessed.
The report consolidates more than 1,000 security assessments into an unfiltered picture of security gaps – of which 70% were observed to remain unresolved. Larger organizations were found to take 3 times longer to remediate their security issues than do their mid-sized peers. Larger organizations take the longest to remediate (230+ days).
Need to respond
The findings aggregated in the STAR report underscore the need for urgent industry action to ensure continuous monitoring of systems and access, faster remediation of known vulnerabilities, stronger ownership of operational controls, and consistent enforcement of identity and access protections, particularly across third-party environments.
Capabilities such as Zero Trust architectures, conditional access, continuous authentication, and automated compliance monitoring are not yet widely used across the entertainment ecosystem. In highly distributed production environments spanning cloud platforms, remote workforces, and a complex ecosystem of third-party vendors, security gaps can greatly increase the impact of a single compromised credential.
Security compliance correlates with level of difficulty
The STAR dataset shows that non‐compliance is most pronounced in technically complex security layers, including Vulnerability Management, Cryptography, Endpoint Hardening, and Access Management. Third-party risks, such as non-compliance with service-level agreements, were also notable.
“Compliance to security guidelines is particularly challenging for smaller stakeholder organizations,” said TPN President Terri Davies, speaking with Piracy Monitor. “Seventy percent of TPN’s members have less than $5 million in revenue and therefore do not have dedicated security teams. Also, they’re more sensitive to cost.” In response, TPN offers discounted access to test lab resources for those without the resources to build and run their own.
Because these more-complex safeguards tend to be more resource-intensive, these areas also exhibit the largest gaps between perceived and validated performance, alongside higher rates of remediation refusal rates and longer remediation timelines.
To single out one example, non-compliance with best-practices around end-point hardening was rated at 32%, and the average time to remediation can be as much as 5 months (up to 149 days).
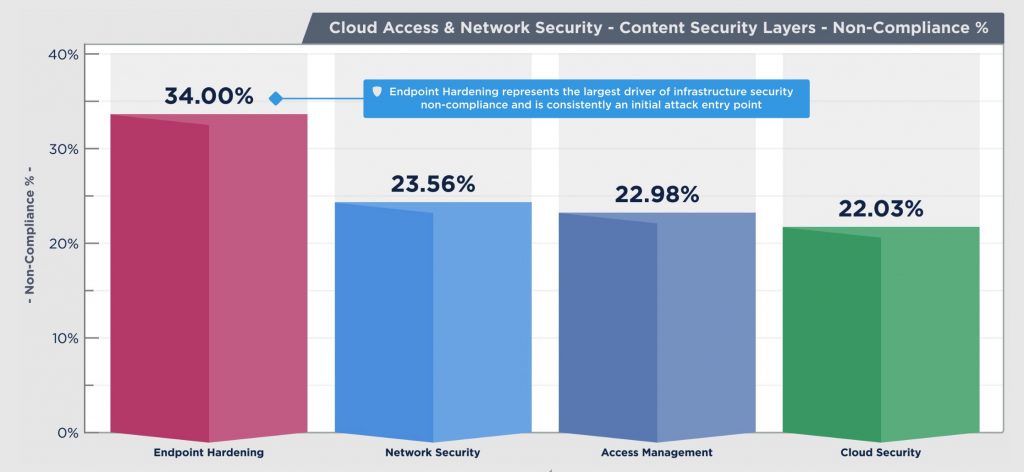
Cloud Access & Network Security risk is driven by execution gaps, with Endpoint Hardening as the leading weakness with variation emerging by organization size and region. (Source: TPN)
Why it matters
Recapping the STAR Report’s main recommendations, security should be treated as a daily responsibility, overseen by a team of professionals that have executive support in identifying and assessing risks, fixing high-risks gaps quickly, holding vendors and partners responsible; and to respond as quickly as possible to security gaps.
“The TPN STAR Report highlights a persistent disconnect between perceived security and actual operational performance,” said Terri Davies, President of TPN. “Organizations routinely overestimate that their controls are effective, especially those that require continuous attention, technical rigor, and operational ownership. Recent technological advances only heighten the urgency to address these gaps before they are exploited,” she said.
Piracy Monitor has long advocated a full-spectrum view of security across content, services, software, devices, transport, data centers and resources accessed in the cloud. By dealing with these risks, negative impact to reputations and to consumers will be reduced.
Further reading
New report from the MPA’s content security initiative links control failures to content security incidents across the entertainment industry. Press release. April 28, 2026. Trusted Partner Network, Motion Picture Association











